The topic How to Configure AWS Cognito for SSO: A Step-by-Step Guide is currently the subject of lively discussion — readers and analysts are keeping a close eye on developments.
This is taking place in a dynamic environment: companies’ decisions and competitors’ reactions can quickly change the picture.
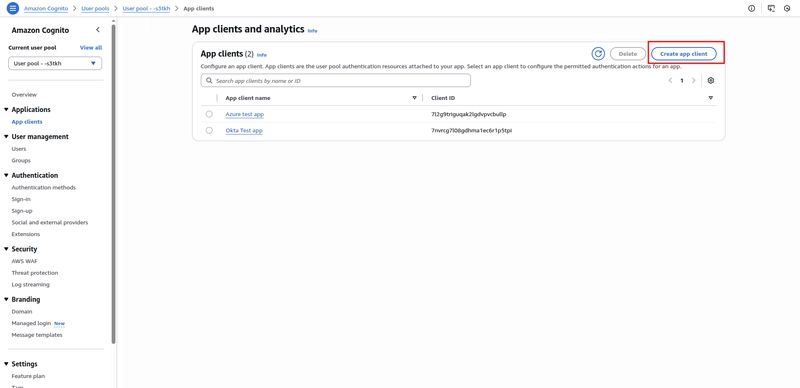
according to the data the multi-tenant application model, we need to create a separate Cognito App Client for each customer and attach their corresponding external OIDC providers.
To create App Client navigate to Application – App client, click to Create App Client
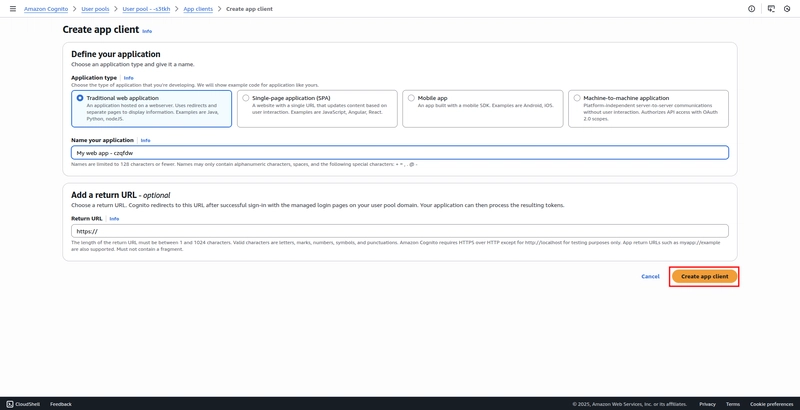
In the setup form, choose Traditional web application as the application type.
To include user groups in the ID token, we need to add a custom attribute to the Cognito User Pool.
In the form, enter the attribute name as shown below, and then click Save changes.
If “roles” scope is configured in Customer OIDC provider, you can add a custom “roles” attribute as well and include this attribute in External Cognito Provider.
!important: In the form, enter the OpenID Connect attribute to groups exactly as shown below, and then click Save changes.
Clarification: We configure these attributes so that the group and role information (optional) is included in the ID Token returned by the Identity Provider. If your application uses different scope names, make sure to update the values in the Cognito accordingly (for example, if Provider sends roles under app_groups scope, you should set OpenID Connect attribute to app_groups).
Info: If you added a “custom:roles” attribute in the previous step, you can include the “roles” attribute here as well.
or http://localhost:8000/api/oidc/cognito/callback/ for local testing).
After custom attributes setup check in Attribute Permission that Read and Write permissions are checked:
After creation, the login page for your App Client will become available and can be accessed directly via its generated URL.
To enable Cognito login for your users in your application, you need to retrieve the following three parameters:
You can find this data on our Cognito User Pool and App client pages.
To copy Client ID and Client Secret Navigate to corresponding App client:
✅ Cognito Setup Complete. Your Cognito configuration is now complete and ready for SSO testing.
Templates let you quickly answer FAQs or store snippets for re-use.
Are you sure you want to hide this comment? It will become hidden in your post, but will still be visible via the comment’s permalink.
For further actions, you may consider blocking this person and/or reporting abuse
Thank you to our Diamond Sponsors for supporting the DEV Community
Google AI is the official AI Model and Platform Partner of DEV
DEV Community — A space to discuss and keep up software development and manage your software career
Built on Forem — the open source software that powers DEV and other inclusive communities.
We’re a place where coders share, stay up-to-date and grow their careers.